I bought a used car this past weekend for my two teenagers to share, for school, work, getting around town, etc. It is a sensible car, four-wheel drive, high safety rating, decent gas mileage, few options and fewer distractions, a big difference from the ’72 TransAm I had as a teenager. Like the car I got for my children the TransAM was 10 years old when I bought it but that’s where the similarities ended.
The ’72 TransAm came in blue with white stripes or white with blue stripes. It was raw power, the new honeycomb grille airflow augmenting the rear facing hood scoop to feed the Rochester Quadrajet 4-bbl carburetor. Every month I scanned my Hot Rod magazine to see if there was some new speed or horsepower tip in one of the columns.
I miss that car; you could do so many things with it. Not only could you service it yourself, there were loads of aftermarket parts and services to take advantage of, I liked that I wasn’t locked into the manufacturer or even have to worry about a specific dealer, it was so easy. And it was my very first hybrid… when I added Nitrous! (I believe that counts as hybrid)
Cisco’s Intercloud Fabric (ICF) reminds me of my TransAm (I’m sure you were wondering how I was going to make the transition to Hybrid Cloud). How so? Well ICF is not locked into a specific cloud provider or their virtual machine format. In the enterprise, ICF can run on Hyper-V, KVM + OpenStack and VMware vSphere. The cloud provider can be running VMware, Hyper-V, OpenStack, CloudStack, ICF works with all those cloud management systems. Plus with the current release 2.2.1, ICF packs in a bunch of new capabilities.
Release 2.2.1 of Intercloud Fabric contains the following new features and enhancements:
That is quite a few items; I want to go over a few briefly and then a couple in detail.
The ICF 2.2.1 release supported operating systems has more than doubled over the previous release and had added multi-disk support
This is really good news as more OS support is being added with every release, there is sure to be a fit with every enterprise.
With a built in trial license for 60 days and 20 Hybrid Cloud Units (HCUs) ICF 2.2.1 has removed all barriers to Hybird cloud in your enterprise! A built in trial license means that you can immediately connect to a cloud provider and migrate VMs. Each VM migrated to or instantiated at a cloud provider is going to utilize one or two HCUs. AWS and Azure will consume two HCUs, while all other cloud providers will consume one. The built in trial license supports all ICF features and services, e.g. Firewall, Router, Integrated Router, VM Onboarding, Netflow, ERSPAN, etc.
The ICF secure network extension AKA the site-to-site tunnel allows you extend your Data Center networking out to the provider cloud. In the previous releases of ICF the site-to-site tunnel required ports 6644 and 6646 be open for Internet traffic. Now with HTTPS support for the site-to-site tunnel port 443 is utilized, which is typically open in an enterprise, making demo or proof-of-concept deployments very quick and easy to implement. It is recommended however that when you move your ICF deployment to production that you do utilize ports 6644 and 6646.
There are really no restrictions on the product utilization, this means that once you’ve deployed with the 60 day license, when you decide to make the deployment permanent all that is required is a license upgrade.
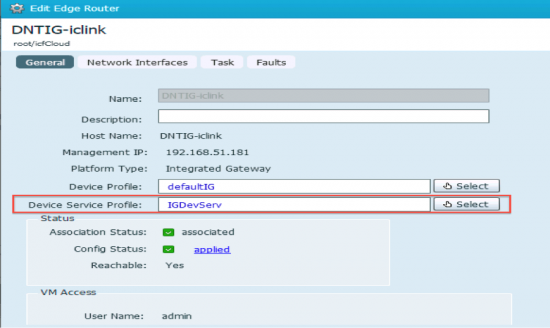
The Intercloud Fabric Router (Integrated – IR) is now supported on Microsoft Azure. The IR provides routing functionality directly in the ICF Intercloud Switch (ICS). Recall that the ICS is the cloud provider side of the site-to-site tunnel extended from the enterprise ICF Intercloud Extender (ICX). The ICX + ICS pair form the secure network extension referred to as the IcfCloud.
When deploying an IcfCloud to Azure a Service selection form is presented for the selection of “ICF Firewall (VSG)” and “ICF Router (Integrated)
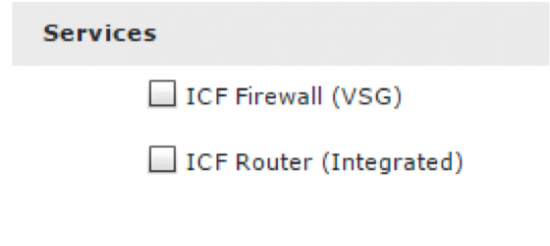
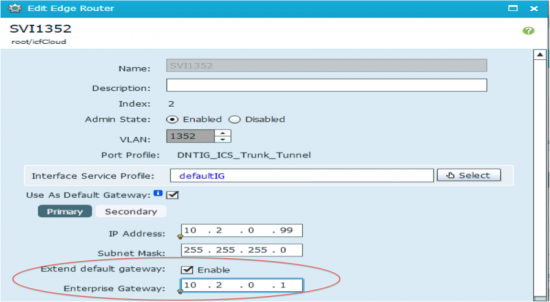
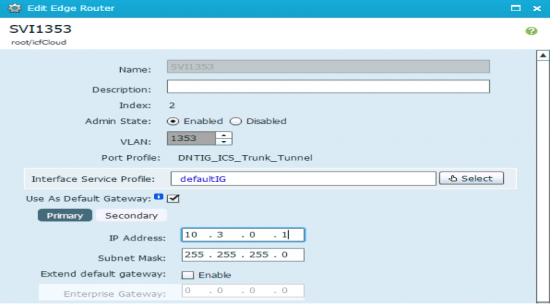
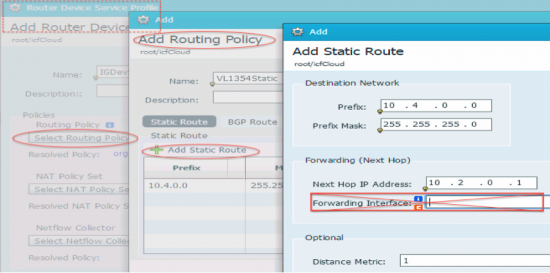
Selecting the ICF Router (Integrated) will cause an “Edge Router” configuration to be created in the Prime Network Services Controller (PNSC) that is deployed as part of the ICF Infrastructure. Through this “Edge Router” configuration in PNSC you can create configure the following ICF IR scenarios
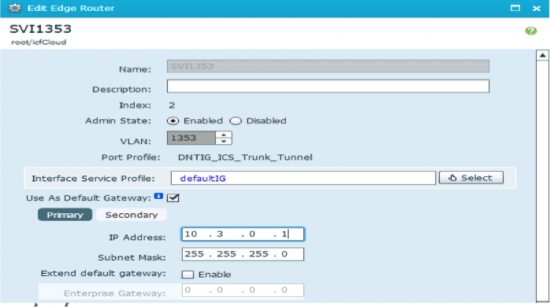
- Accomplish this by creating sub-interfaces on the IR – One for each VLAN to be routed
- Created sub-interfaces are assigned the IP address of the default gateway for each subnet
- e.g. VLANs 1352 and 1353 only have VMs in the Cloud
- VLAN 1352 – subnet 10.2.0.1/24 – IR gateway – 10.2.0.1
- VLAN 1353 – subnet 10.3.0.1/24 – IR gateway – 10.3.0.1
The Integrated Router also supports Static NAT and Dynamic NAT, for a detailed explanation of implementing these NAT types in the IR be sure to attend my Cisco Live San Diego Breakout session, BRKCLD-2003
Since the IR functionality is built into the ICS that’s one less VM required in the provider cloud to support the routing and NAT features you’ll want to utilize. Initial IR deployment is a clicking a checkbox during a guided workflow, it really couldn’t be simpler!
The other new feature that I wanted to highlight is VM onboarding. For AWS VMs that already exist in either a default VPC or a user defined VPC can now be brought into the secure ICF shell and have the ability to communicate over the secure network extension. This is a huge boon for those customers that wish to connect to and bring shadow IT under control, as well as workloads that are just sitting out in Amazon.
Prior to release 2.2.1, VMs that have previously been deployed in AWS were not accessible to VMs in the secure ICF shell. The 2.2.1 release introduces the capability to onboard these VMs. VM onboarding is a great new feature and will work well provided the following criteria are met:
Shadow IT is hidden costs, shadow IT is potential security breeches, shadow IT is loss of control. Shadow IT arises from process and controls put in place to stop the very scenarios just mentioned from taking place. Providing users a way to get the resources they need as quickly as they need them by using hybrid cloud through ICF you’ve taken the first step to controlling shadow IT.
Cisco Intercloud Fabric 2.2.1, is feature packed with what our customers have asked for to make Hybrid Cloud a reality in their enterprise.
I’ll be presenting several sessions at Cisco Live along with my coworkers be sure to attend one or more.
PSOCLD1001 – Hybrid Cloud with Intercloud Fabric – Percy Wadia
TECCLD3001 – Intercloud Fabric Technical Deep dive – Mauricio Arregoces
DEVNET-2009 – Intercloud Fabric REST APIs for Providers – Paulo Renato DaSilva
DEVNET-1120 – Intercloud Fabric – AWS and Azure Account Setup and Utilization – John McDonough
DEVNET-1008 – Private or Public or Hybrid ? Which Cloud Should I choose?
DEVNET-1009 – Cisco Intercloud Fabric for Business, Helping Enterprises Move to Hybrid Cloud! – Chhavi Nijhawan
Not and Intercloud session but something I know really well.
DEVNET-1119 – UCS PowerTool Secrets – Tips and Tricks – John McDonough